Threat Actor Characterization

Chinafans
ID: 240e334e84f2374ccb21f933726fe1c373689| 0x | 0x_Fans | 0***** | ad******* |
| ch******* | we******** | — | — |
Actor Network Graph
Open Network GraphMITRE ATT&CK®
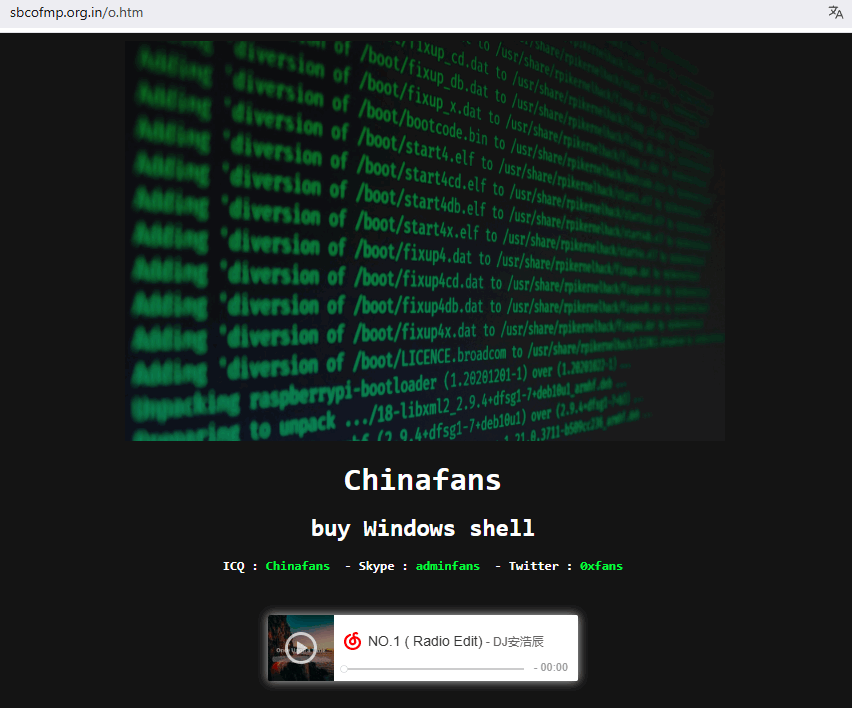
“chinafans” — administrator of the 0xTeam Network and prolific web-defacer whose mirrors on Zone-H/Zone-Xsec show trademark drop-files such as 0x.txt, o.htm, and xx.htm across many targets. Operates/sells via the ‘0xTeam-Network’ Telegram channel and maintains a public presence; also joined the TurkHackTeam forum as a new member on 26 Nov 2023.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1491.002 | External Defacement | TA0040 |
|
| T1585 | Establish Accounts | TA0042 |
|
| T1588 | Obtain Capabilities | TA0042 |
CLASSIFICATION: Unclassified / Open Source
Executive Summary
“chinafans” appears in multiple defacement archives as a prolific notifier associated with the 0xTeam Network, repeatedly leaving distinctive drop-files such as 0x.txt, o.htm, and xx.htm on compromised sites. Public artifacts include thousands of Zone-H/Zone-Xsec mirrors showing these filenames across diverse targets and a Telegram channel (“0xTeam-Network”) that advertises “random shells” for sale and links to the notifier’s mirror records. In late 2023, the handle joined the TurkHackTeam (THT) forum as a new member, with a visible profile and intro thread. The OSINT does not prove a larger staffed collective behind 0xTeam; signs suggest a single administrator with possible ad-hoc collaborators (INFERENCE, confidence: low–medium). Overall, the evidentiary base strongly supports persistent external defacement activity and capability monetization; technical vectors for initial access are unspecified in public mirrors.
- 2016-04–10. Early mirrors show xx.htm/related patterns on multiple hosts (representative entries via IP archives).
- 2016-07-17. wegielkrapkowice.pl/xx.htm recorded by Zone-H (notified by “chinafans”).
- 2017-09-03. himalayafairreisen.com/o.htm defacement mirror saved.
- 2019-04-21. ugc.com.sa/o.htm defacement mirror saved.
- 2021-09-08. cpedu.in/o.htm defacement mirror saved.
- 2023-11-26–27. TurkHackTeam forum: account “chinafans” joins (profile + “Hello, Chinafans” thread).
- 2024. Telegram 0xTeam-Network posts include live links and pricing lists; channel tagline advertises selling shells.
- 2024–2025. Zone-H/Zone-Xsec show sustained activity with /0x.txt across many domains (representative pages).
- 2025-10-08. Zone-Xsec attacker page lists current wave of /0x.txt mirrors under team tag “0xteam.”