Threat Actor Characterization

Cicada3301
ID: 11196e28e27f5da7fabf6449326a641101089| Cicada 3301 | — | — | — |
Actor Network Graph
Open Network GraphMITRE ATT&CK®
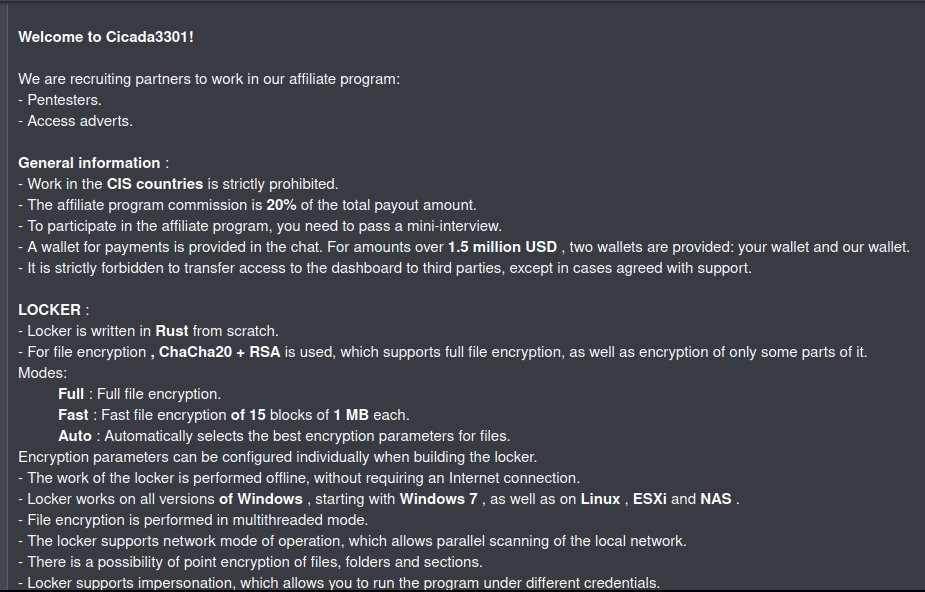
Cicada3301 is publicly described as a ransomware-as-a-service (RaaS) ecosystem that emerged in 2024, operating a double-extortion workflow supported by a leak/negotiation site and affiliate recruitment. Technical reporting describes a Rust-based, cross-platform encryptor targeting Windows and Linux, with some reporting emphasizing ESXi environments.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1190 | Exploit Public-Facing Application | TA0001 |
|
| T1078 | Valid Accounts | TA0001 TA0003 TA0004 TA0005 |
|
| T1105 | Ingress Tool Transfer | TA0011 |
|
| T1059.001 | PowerShell | TA0002 |
|
| T1569.002 | Service Execution | TA0002 |
|
| T1021.001 | Remote Desktop Protocol | TA0008 |
|
| T1047 | Windows Management Instrumentation | TA0002 |
|
| T1490 | Inhibit System Recovery | TA0040 |
|
| T1489 | Service Stop | TA0040 |
|
| T1486 | Data Encrypted for Impact | TA0040 |
|
| T1041 | Exfiltration Over C2 Channel | TA0010 |
|
| T1567.002 | Exfiltration to Cloud Storage | TA0010 |
|
Cicada3301
Classification: Unclassified / Open Source Intelligence (OSINT) — TLP:WHITE
Executive Summary
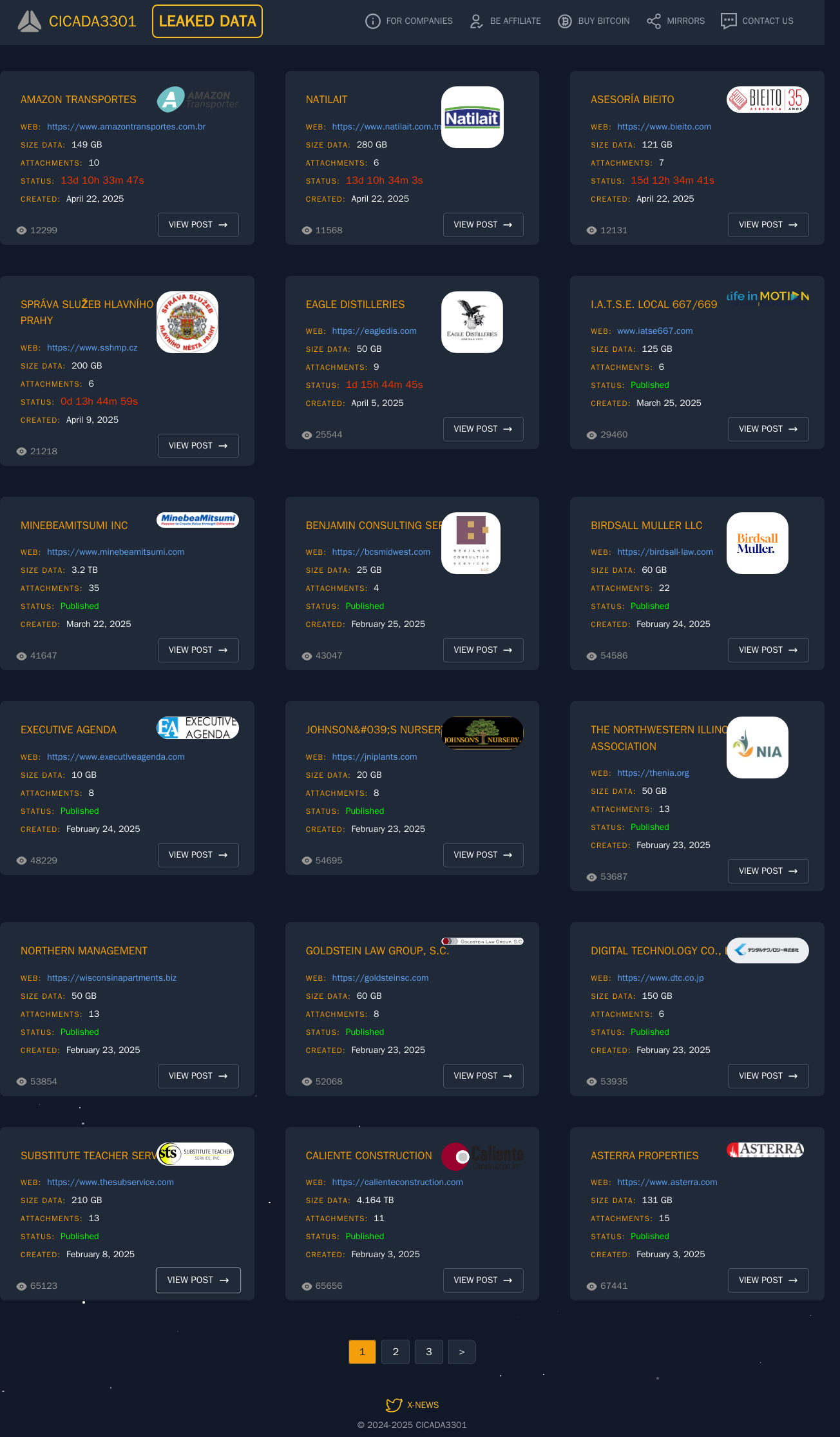
Cicada3301 is publicly described as a ransomware-as-a-service (RaaS) operation that emerged in mid‑2024 with a leak site supporting double extortion. Public technical reporting describes a Rust-based encryptor with cross-platform targeting that includes Windows and Linux, with some reporting explicitly calling out ESXi environments as part of the target surface. Reporting also describes an affiliate program model where operators provide infrastructure and tooling while partners conduct intrusions and deploy the encryptor for impact.
Cicada3301 is modeled as a crimeware RaaS ecosystem rather than an ideological actor. The operating logic is consistent with multi-extortion ransomware: unauthorized access, data theft for leverage, then encryption for disruption and pressure.