Threat Actor Characterization

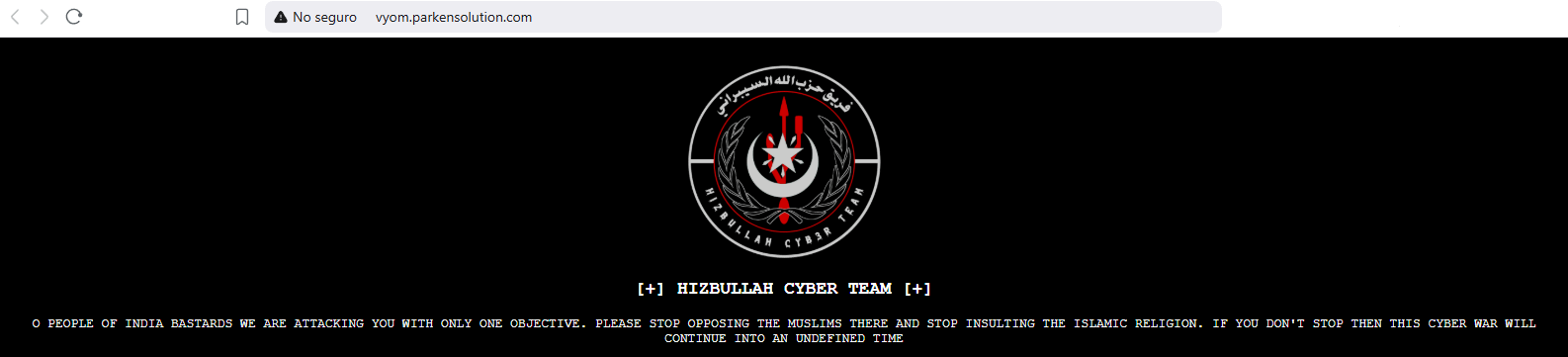
Hezbollah Cyber Group
ID: 03334cb4ca6bc8cc196742d5901bda2e26640| HCG | HCT | Hi****************** | Hi******************* |
| HI****************** | HI****************** | hi********************* | Hi**************** |
Actor Network Graph
Open Network GraphCLASSIFICATION: Unclassified / Open Source
Executive Summary
“Hezbollah Cyber Group” is best understood not as a single monolithic unit but as a cluster of Lebanon-based or Hezbollah-aligned cyber entities that span espionage APTs (e.g., Volatile/Lebanese Cedar; POLONIUM / Plaid Rain) and propaganda/ops fronts seen during the 2023–2025 Israel war cycle (e.g., Radwan Cyber Pal, NetHunt3r). Public technical reporting attributes telecom/ISP intrusions and custom tooling (e.g., Caterpillar web shell, Explosive RAT) to Lebanese Cedar since at least 2012, and documents POLONIUM’s 2022–2023 campaigns against Israeli sectors. Microsoft further assessed in 2024–2025 that Iran–Hezbollah collaboration in cyber/influence operations intensified, while 2024–2025 narratives describe Hezbollah-aligned fronts claiming compromises of Israeli ministries and information assets. Overall: capability varies from low-soph hacktivism to persistent espionage; intent focuses on collection, psychological impact, and pressure on Israel. Confidence: medium (primary vendor reports + think-tank corroboration).
- Ecosystem construct. Credible sources describe Lebanese Cedar (Volatile Cedar; MITRE G0123) as a Lebanese threat group linked in open sources to Hezbollah and active since ~2012 (worldwide victims; heavy focus on Israel and telecoms/hosting).
- Additional node (POLONIUM / Plaid Rain). Microsoft (2022) exposed POLONIUM (now Plaid Rain) as Lebanon-based, primarily targeting Israeli organizations; assessed coordination with Iran MOIS-affiliated actors.
- Propaganda fronts. 2024–2025 analyses cite Hezbollah-aligned “fronts” (e.g., Radwan Cyber Pal, NetHunt3r) claiming ministry-level compromises and document dumps—high propaganda value; varying technical depth.
- Iran link. Microsoft (Feb 2024) described increasing Iran–Hezbollah collaboration in cyber/influence ops during the Gaza war, suggesting tighter operational proximity.